Photo by Hillary Ehlen
By Jamie Maguire
Presented by High Point Networks
High Point Networks is a value-added reseller (VAR) of information technology providing solutions to both the SMB and enterprise level markets in the upper Great Plains. They offer organizations best-in-class voice and data networking solutions, supported by the best professional services team in the region. Their solutions solve real challenges and provide measurable return on investment.
As a penetration tester, I am tasked with testing a company’s cyber security by attempting to penetrate the network, or in other words, ethically hacking the network. The idea is to think like the bad guys and try to hack into a company to identify weaknesses before the bad guys find them. This often includes a lot of scanning and maybe some exploiting, but my favorite thing to go after is passwords. If I can guess or steal your password, then as far as a computer or application is concerned, I am you.
1. Check yourself
Security Researcher and Microsoft MVP, Troy Hunt, runs a website called “Have I been pwned?” Troy collects and aggregates data breaches and allows you to search them by visiting HaveIBeenPwned.com. In addition, the site will allow you to search for compromised accounts by domain. For example, if I can prove I am from High Point Networks, the site will provide a report of anyone in a data breach with an “@highpointnetworks.com” email address. This can be useful for educating staff and coworkers on the risks of password reuse. Troy’s site also provides a search for compromised passwords. So, you could enter a password and see if it shows up in any data breaches. However, I never recommend throwing any of your current passwords into any websites that claim to check the strength of your password or something like this. If you think your password may be compromised, you should change it first then enter the old password into Troy’s website.
2. Turn on MFA
Multifactor Authentication, or MFA, is a second layer of security required to log into an account. This may be a PIN delivered by text message or phone call, or a separate app on your cell phone that prompts you with a push notification. The advantage to MFA is that, even if a scammer has your username and password, they will not be able to access your accounts without the second factor. At a minimum, consider using MFA on social media sites such as Facebook, Twitter and Instagram. All banking, shopping sites such as Amazon and personal email such as Yahoo or Gmail are a must for MFA. Most common websites support MFA. Visit TwoFactorAuth.org for a complete listing of websites that support MFA.
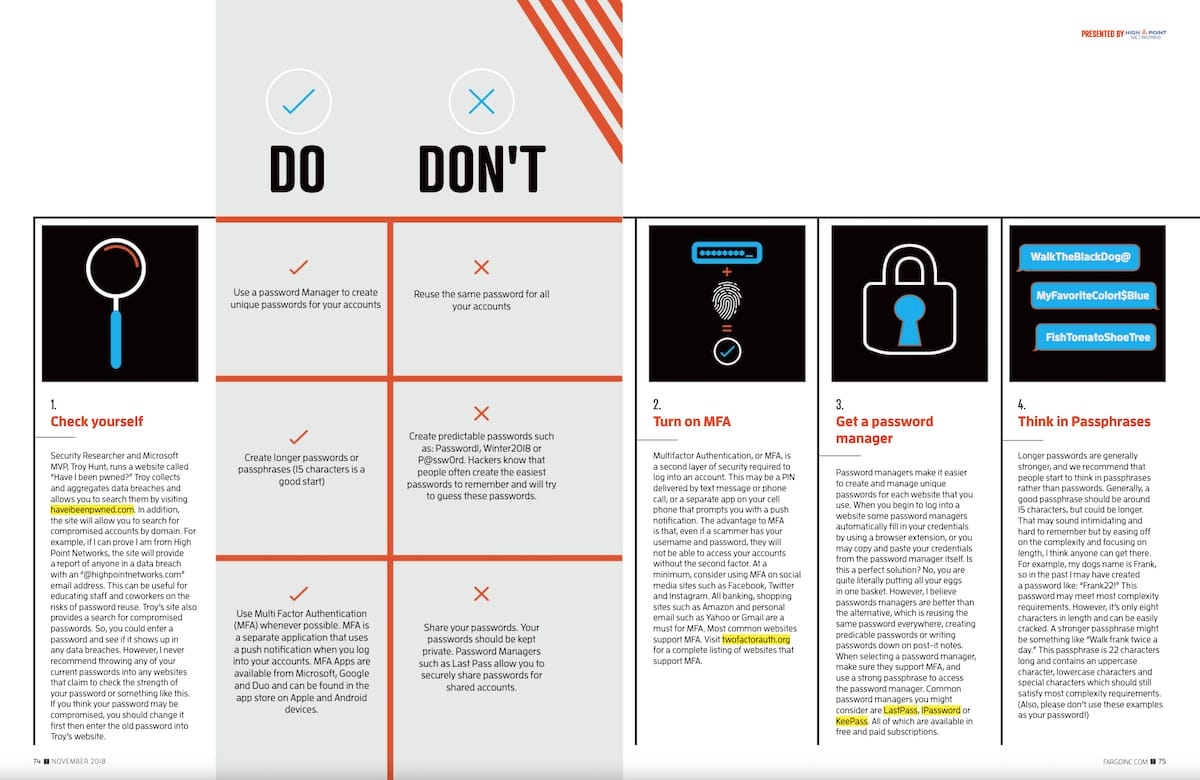
Do:
- Use a password Manager to create unique passwords for your accounts
- Create longer passwords or passphrases (15 characters is a good start)
- Use Multi Factor Authentication (MFA) whenever possible. MFA is a separate application that uses a push notification when you log into your accounts. MFA Apps are available from Microsoft, Google and Duo and can be found in the app store on Apple and Android devices.
Don’t:
- Reuse the same password for all your accounts
- Create predictable passwords such as: Password1, Winter2018 or P@ssw0rd. Hackers know that people often create the easiest passwords to remember and will try to guess these passwords.
- Share your passwords. Your passwords should be kept private. Password Managers such as Last Pass allow you to securely share passwords for shared accounts.
3. Get a password manager
Password managers make it easier to create and manage unique passwords for each website that you use. When you begin to log into a website some password managers automatically fill in your credentials by using a browser extension, or you may copy and paste your credentials from the password manager itself. Is this a perfect solution? No, you are quite literally putting all your eggs in one basket. However, I believe passwords managers are better than the alternative, which is reusing the same password everywhere, creating predicable passwords or writing passwords down on post-it notes. When selecting a password manager, make sure they support MFA, and use a strong passphrase to access the password manager. Common password managers you might consider are LastPass, 1Password or KeePass. All of which are available in free and paid subscriptions.
4. Think in Passphrases
Longer passwords are generally stronger, and we recommend that people start to think in passphrases rather than passwords. Generally, a good passphrase should be around 15 characters, but could be longer. That may sound intimidating and hard to remember but by easing off on the complexity and focusing on length, I think anyone can get there. For example, my dogs name is Frank, so in the past I may have created a password like: “Frank22!” This password may meet most complexity requirements. However, it’s only eight characters in length and can be easily cracked. A stronger passphrase might be something like “Walk frank twice a day.” This passphrase is 22 characters long and contains an uppercase character, lowercase characters and special characters which should still satisfy most complexity requirements. (Also, please don’t use these examples as your password!)
High Point Networks
728 E Beaton Dr, West Fargo